Ledger.com/Start is the official onboarding page designed to help users securely set up Ledger hardware wallets and begin managing cryptocurrency with confidence. Ledger is widely recognized as a leader in hardware wallet technology, offering tools that enable true self-custody of digital assets. This page serves as an educational, unofficial guide that explains how Ledger.com/Start works, what users should expect during setup, and how to safely manage crypto assets using Ledger devices.
What Is Ledger.com/Start?
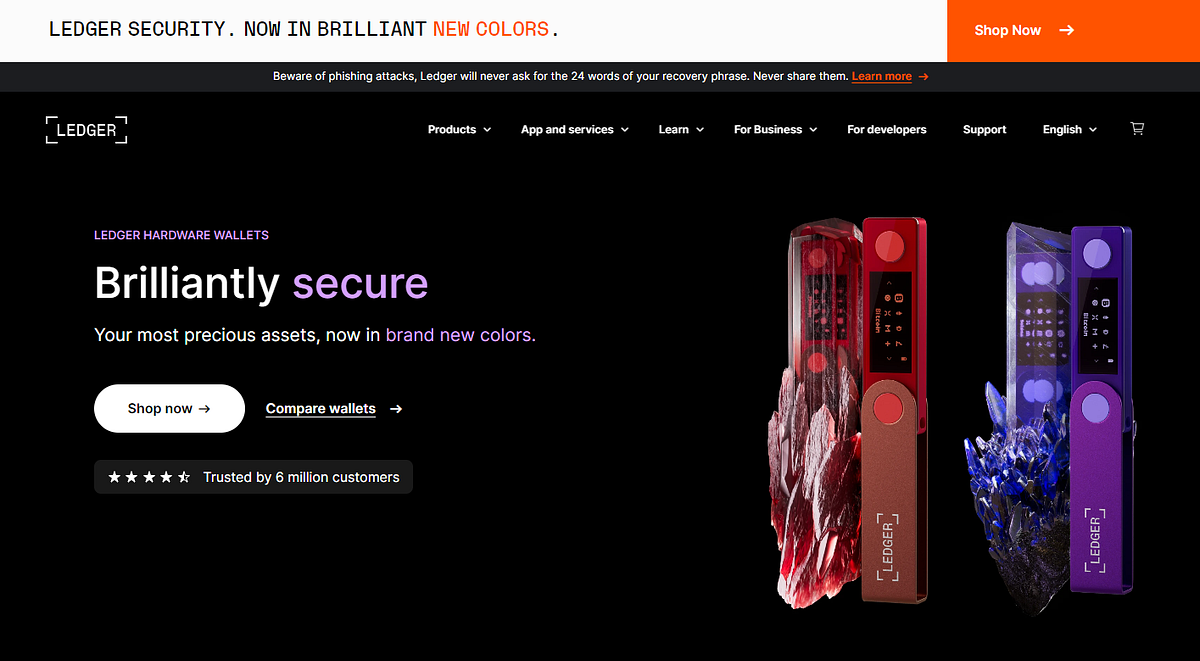
Ledger.com/Start is the primary entry point for new Ledger users. It provides step-by-step instructions for initializing Ledger hardware wallets such as Ledger Nano S Plus and Ledger Nano X. The purpose of this page is to ensure that users follow secure practices from the very beginning, minimizing the risk of errors, scams, or security breaches.
Understanding Ledger Hardware Wallets
Ledger hardware wallets are physical devices that store private keys offline. This means your private keys never leave the device, even when connected to a computer or mobile phone. By isolating keys from internet-connected environments, Ledger significantly reduces the risk of hacking, malware attacks, and phishing attempts.
Why Ledger.com/Start Is Important
Visiting Ledger.com/Start ensures that users download authentic Ledger software and follow verified setup procedures. Many crypto losses occur due to fake websites or unofficial downloads. Using the official start page helps protect users from counterfeit apps and malicious firmware.
Initial Setup Process
When starting with a new Ledger device, users are guided through connecting the hardware wallet to a computer or mobile device. During setup, the device prompts the user to create a secure PIN code. This PIN protects the device from unauthorized access if it is lost or stolen.
Recovery Phrase Explained
One of the most critical steps in the Ledger.com/Start process is generating the recovery phrase. This phrase usually consists of 24 words displayed directly on the Ledger device screen. It acts as a master backup that can restore access to funds if the device is damaged or replaced.
The recovery phrase must be written down and stored offline. It should never be photographed, uploaded to cloud storage, or shared with anyone. Anyone with access to this phrase can control the wallet’s funds.
Using Ledger Live
Ledger Live is the companion application used to manage crypto assets. Once the device is initialized, users install Ledger Live to view balances, send and receive cryptocurrency, install blockchain apps, and track portfolio performance. Ledger Live acts as a dashboard while all sensitive actions are confirmed directly on the hardware device.
Supported Cryptocurrencies
Ledger supports thousands of cryptocurrencies, including Bitcoin, Ethereum, Litecoin, and many ERC-20 tokens. Users can install multiple blockchain apps on their device and manage different assets simultaneously. This flexibility makes Ledger suitable for beginners and advanced crypto users alike.
Sending and Receiving Assets
To send cryptocurrency, users initiate the transaction in Ledger Live and confirm the details on the Ledger device screen. This verification step ensures that the transaction address and amount are correct, even if the computer is compromised.
Receiving assets is equally simple. Ledger Live generates a receiving address that must be confirmed on the device. This ensures that the address displayed has not been altered by malicious software.
Security Best Practices
- Always access setup instructions through Ledger.com/Start.
- Never share your recovery phrase or PIN.
- Store recovery phrases in a secure, offline location.
- Verify transaction details directly on the Ledger device.
- Keep Ledger Live and firmware updated.
Firmware Updates
Ledger periodically releases firmware updates to enhance security and add features. These updates are managed through Ledger Live and require confirmation on the device. Keeping firmware up to date ensures protection against newly discovered vulnerabilities.
Using Ledger with DeFi and Web3
Ledger devices can connect to decentralized applications (dApps) and Web3 platforms through supported wallets and browser extensions. This allows users to participate in DeFi, staking, and NFT activities while maintaining hardware-level security.
Backup and Recovery
In the event of device loss or failure, users can restore their wallet using the recovery phrase on a new Ledger device or compatible wallet. This highlights the importance of safeguarding the recovery phrase at all times.
Who Should Use Ledger?
Ledger is ideal for users who value security, self-custody, and long-term asset protection. Whether holding crypto as an investment or actively using Web3 services, Ledger provides a secure foundation for managing digital assets responsibly.
Conclusion
Ledger.com/Start is the safest way to begin using a Ledger hardware wallet. By following official instructions, understanding recovery procedures, and practicing strong security habits, users can confidently manage their cryptocurrency. This guide serves as an educational overview to help users understand the setup process and the importance of hardware wallet security in today’s digital asset ecosystem.